HTTP vs HTTPS
HTTP vs. HTTPS provides an overview of the history and implementation, including how to use HTTP vs. HTTPS and why Google is pushing all websites to be HTTPS.
In 1957, the first satellite was launched into orbit. At this time, the United States had focused on making better cars and bigger television sets. On the contrary, the Soviets were focused on the Cold War and wanted to win. The Soviets named their satellite Sputnik. After that, the United States added chemistry, physics, and calculus to higher education. The military and scientists thought that the Soviet Union could attack the United States using its missiles to destroy the network of telephone lines and wires for long-distance communication.
In 1962, Mr. J.C.R. Licklider, a scientist from M.I.T. who worked for the Department of Defense Advanced Research Projects Agency (ARPA), developed space-age rockets, weapons, and computers. Mr. Licklider had proposed a solution: the Galactic Network. This type of network would allow government leaders to communicate if the Soviets destroyed the telephone system.
Packet Switching
In 1965, another M.I.T Scientist named Leonard Kleinrock, the other father of the Internet, developed a packet-switching network. Packet-switching takes data and breaks it down into blocks or packets before it reaches its destination. Each packet will take its route from one place to another place. The government’s computer network did not allow packet switching. The network that the US government used was called ARPANET. Hence, this was left for enemy attacks. In 1969, ARPAnet sent its first message from one computer to another computer (Node-to-Node). The computer was located at the UCLA research lab.
1970 Network Grows
Toward the end of 1969, only four computers were connected to ARPANET, but 1970 the network was growing. Also, in 1970, another computer scientist named Vinton Cerf was born. Mr. Cerf. was a program manager with the U.S. Department of Defense’s Advanced Research Projects Agency (DARPA). This is where he fostered the development of Internet-related packet data and security technologies. During the same year, the University of Hawaii installed ALOHnet, and in two years, London University College and the Royal Radar Establishment in Norway joined this grid.
Here comes Netscape
After a few years, Mr. Cerf added another Protocol. This Protocol was known as Internet Protocol, which uses TCP/IP. This protocol is known as the Handshake. In 1992, researchers and students at the University of Illinois developed Netscape (Browser). Netscape allowed people to access the Internet and simultaneously see words and pictures on the same page. Also, Congress used the web to promote their commercials. This became an excellent way to reach out to customers and sell goods. Each page existed because of Hypertext Transfer Protocol (HTTP). Mr. Berners-Lee proposed HTTP.
HTTP Development
HTTP is the standard language for the World Wide Web (WWW). The reason for developing HTTP was that it would work with other browsers. The HTTP started as a single keyword and Document path for browsers and Internet-connecting software and hardware applications. Mr. Berners-Lee outlined the motivation for the new protocol and was listed with high-level design goals, such as file transfer functionality, requesting an index search of a hypertext archive, format negotiation, and referring the client to another server. Hence, a simple prototype was built. It implemented a small subset of the proposed function. They include a client who requests a single ASCII character string also terminated by a carriage return (CRLF), a server response in an ASCII character stream, a hypertext markup language (HTML), and a connection terminated after the complete document transfer.
This path ID has a single line: GET method. It is the response to a single hypertext document, meaning no heading or other Metadata, only the HTML tag.
HTTP Improvements
Around the same time, a parallel HTTP Working Group (HTTP-WG), the IETF, focused on improving the HTTP protocol. Between 1994 and 1995, there was dial-up Internet access for the public. August 9, 1995, was the first day of the Internet, along with its popularity. With the growth of the web, a community of web developers has produced many experimental HTTP server and client implementations through an ad hoc process: implement and deploy to see if others would adopt it.
In May 1996, the HTTP Working Group (HTTP-WG) published RFC 1945, documenting the “common usage” of the many HTTP/1.0 implementations. This was a period of rapid experimentation, with the best practices and common patterns.
HTTP vs. HTTPS
A simple protocol for quickly retrieving hypertext has become a generic hypermedia transport. The wide availability of clients to consume means that many applications are now designed and deployed exclusively on top of HTTP. HTTP is HTTPS, the secure version of HTTP, the protocol for sending data between the browser and the website.

HTTP vs HTTPS
SSL & TLS
HTTPS, the (S) in HTTP, means that the website that you are visiting is secure. It is secured by using encryption. HTTPS protects confidential online transactions, such as online banking and online shopping order forms. HTTPS pages typically use one of two secure protocols to encrypt communications – SSL (Secure Sockets Layer) or TLS (Transport Layer Security). The asymmetric system uses two ‘keys’ to encrypt communications: a ‘public’ key and a ‘private key. The private key and vice-versa can only decrypt anything encrypted with the public key. The private key should be kept strictly protected and should only be accessible to the private key owner. In the case of a website, the private key remains secure on the webserver.
HTTPS Requests
When an HTTPS is requested, the website sends its SSL certificate to the browser. A certificate contains the public key needed to begin the secure session. Based on this initial exchange, the browser and website initiate the ‘SSL handshake.’ The SSL handshake generates shared secrets to establish a uniquely secure connection between the personal computer and the website. Users will see a padlock icon in the browser address bar when a trusted SSL Digital Certificate is used during an HTTPS connection. The address bar will turn green when an Extended Validation Certificate is installed on a website.
All communications sent over regular HTTP connections are in ‘plain text’ and can be read by any hacker who manages to break the connection between the browser and the website. This presents a clear danger if the ‘communication’ is on an order form and includes personal credit card details or social security numbers. Using an HTTPS connection, all communications are securely encrypted. This means that even if somebody managed to break the connection, they would not decrypt any data between you and the website. From all this, you can see that the comparison of HTTP vs. HTTPS shows why HTTPS is the correct choice.
HTTPS vs. HTTP – Google Perspective
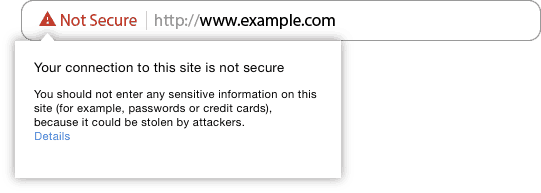
Google is forcing all websites to have SSL certificates. In fact, with the announcement, Google will flag all the unencrypted internet by the end of 2017. Overall, this is one of many parts of a good page experience. Hence, it is paramount that you get an SSL certificate if your business owner runs a website!
If your websites are on HTTP://, then you should contact your hosting company and have them install an SSL.
Summary of HTTP vs. HTTPS
The significant benefits of an HTTPS vs. HTTP include,
- Information is protected, encrypted, and cannot be intercepted.
- Visitors can verify that you are a registered business and own the domain.
- Protection from Cybercriminals.
- Customers are more likely to trust and complete purchases
Transport Layer Security (TLS) to send the information back and forth. When shopping online, always make sure that your page is secure!
References HTTP vs. HTTP
Are you unsure about HTTP vs. HTTPS? Contact us with your website URL, and we’ll provide you with the correct information.
Delivering Effective Web Design & Online Marketing Services
Local Web Design Services for Small Businesses
You've come to the right place if you're looking for web design, website development, a new website, or a revamp of an existing small business website. We understand the needs of business owners and the benefits your website can provide. Besides, we know that, as website owners. You will want to see immediate results.
Furthermore, we can help your website reach an international, national, or local business and customer base. We also know how to get your customers to you. After all, small business website development and SEO know-how are our specialties!
Our customers continually praise our web design services. Check our reviews!
We Deliver Effective Web & SEO Services
Our website developers specialize in delivering exceptional websites, nothing more. Our developers' and marketers' qualifications and experience enable us to provide clear, concise solutions. Whether a website is complex or straightforward, or built on PHP or ASP, we will always keep you informed throughout the web development process.
Visualwebz LLC is the ideal firm to hire for your next project. Immediately after your website is launched, we will work with you to enhance your online presence. For example, our SEO specialists will help drive traffic to your website with this in mind. We will also ensure your web security. Remember, you must protect your website from hackers. Similarly, other website design services include website maintenance, support, and testing.
Are you interested in our services? Do you have questions about our SEO Company, expertise, or web design costs? Then contact us today at (425) 336-0069. You may also want to check our reviews and learn why our customers like us! After all, our 5-star reviews tell prospective customers why we stand out for service, punctuality, quality, and affordability.
Resources & Links
Our Blog covers a range of web resources, services, practices, and trends in web design and SEO.
Marketing & SEO
Web Design & Website Development
- Website redesign.
- Seattle WordPress website design.
- Professional Seattle web design.
- E-Commerce platform.
- Website questions.
- Web Design Trends to Watch Out For.
- Website services.
- Essential website tools.